Home » Microsoft » 98-367 » HOTSPOT
HOTSPOT
Alice and Bob are exchanging messages with each other. Chuck modifies the messages sent between Alice and Bob as shown in the following image:

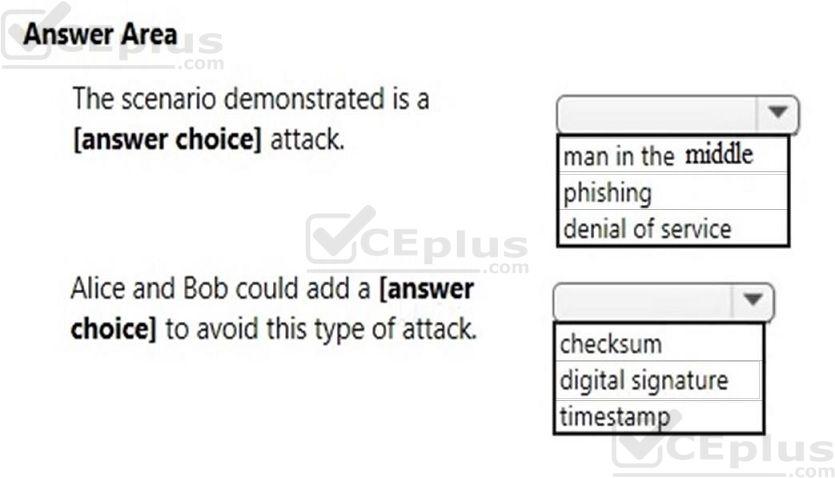
Use the drop-down menus to select the answer choice that completes each statement. Each correct selection is worth one point.
Hot Area:
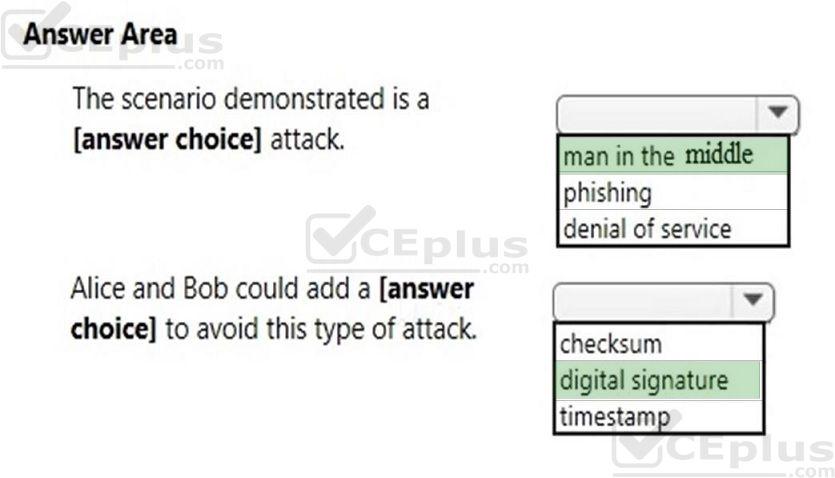
Correct Answer:
Explanation/Reference:
First answer – man in the middle Second answer – digital signature Explanation:
The usual way to prevent the man-in-the-middle attack is to use a public key cryptosystem capable of providing digital signatures. For set up, the parties must know each others public keys in advance. After the shared secret has been generated, the parties send digital signatures of it to each other. The man-in-themiddle can attempt to forge these signatures, but fails because he cannot fake the signatures.