Refer to the exhibit. What is the configuration design to prevent?
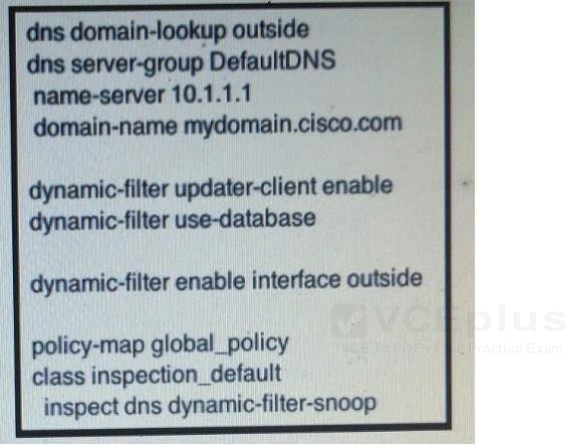
A. Man in the Middle Attacks
B. Dynamic payload inspection
C. Backdoor control channels for infected hosts
D. DNS Inspection
Refer to the exhibit. What is the configuration design to prevent?
A. Man in the Middle Attacks
B. Dynamic payload inspection
C. Backdoor control channels for infected hosts
D. DNS Inspection