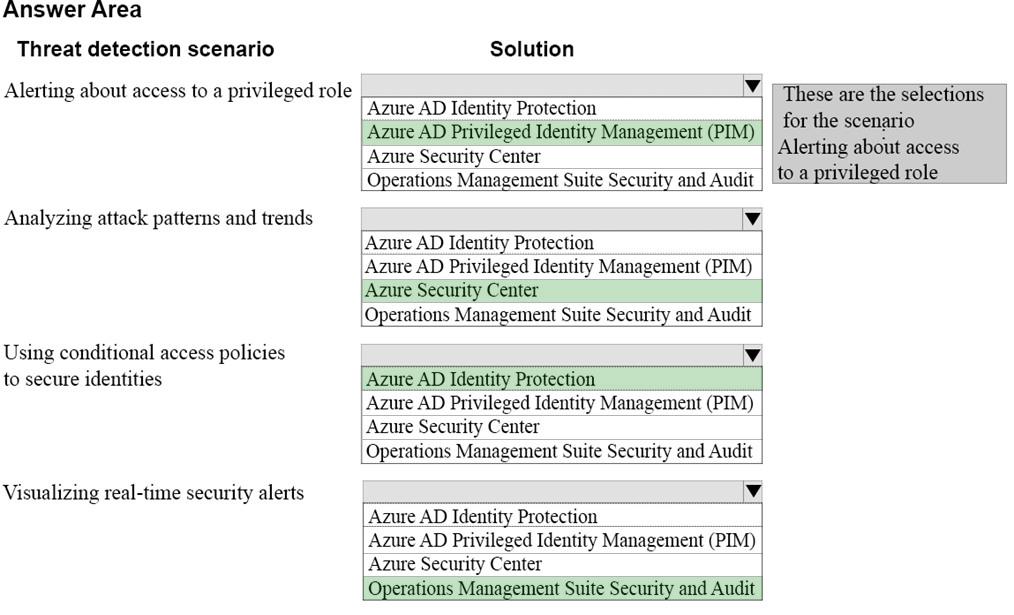
HOTSPOT
You manage a hybrid Azure solution for a company.
You need to recommend Advanced Threat Detection solutions to guard against hacker attacks in different scenarios.
What should you recommend? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:

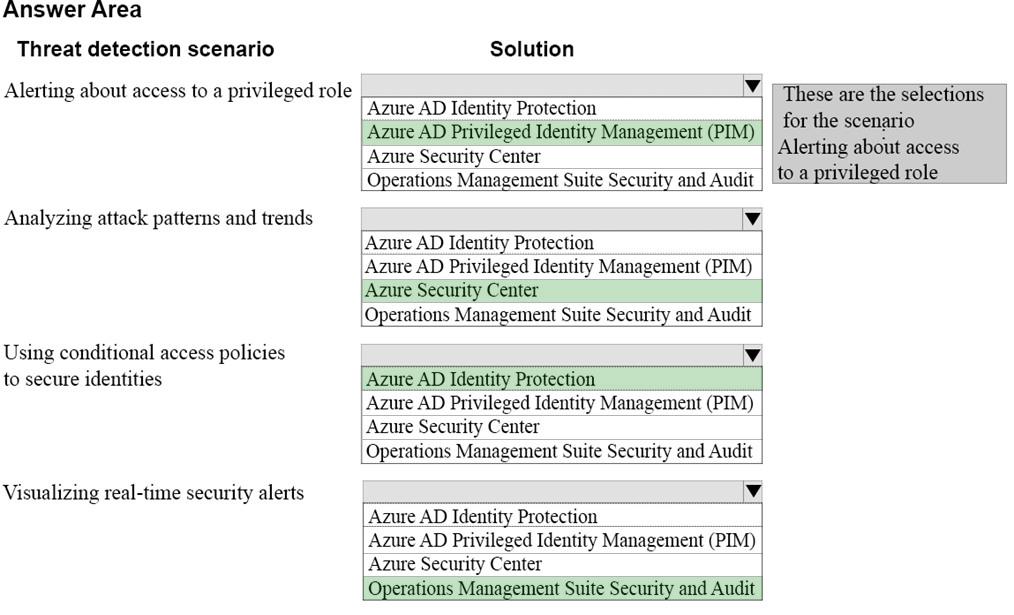
Correct Answer:
Explanation/Reference:
Explanation:
Box 1 (Alerting about access to a privileged role): Azure Privileged Identity Management (PIM)
Azure Privileged Identity Management (PIM) generates alerts when there is suspicious or unsafe activity in your environment. When an alert is triggered, it shows up on the PIM dashboard.
Box 2 (Analyzing attack patterns and trends): Azure Security Center
Every second counts when you are under attack. Azure Security Center (ASC) uses advanced analytics and global threat intelligence to detect malicious threats, and the new capabilities empower you to respond quickly.
Box 3 (Using conditional access policies to secure identities): Azure AD Identity Protection
Security is a top concern for organizations using the cloud. A key aspect of cloud security is identity and access when it comes to managing your cloud resources.
In a mobile-first, cloud-first world, users can access your organization’s resources using a variety of devices and apps from anywhere. As a result of this, just focusing on who can access a resource is not sufficient anymore. In order to master the balance between security and productivity, IT professionals also need to factor how a resource is being accessed into an access control decision. With Azure AD conditional access, you can address this requirement. Conditional access is a capability of Azure Active Directory that enables you to enforce controls on the access to apps in your environment based on specific conditions from a central location.
Box 4 (Visualizing real-time security alerts): Operations Management Suite Security and Audit
The OMS Security and Audit solution provides a comprehensive view into your organization’s IT security posture with built-in search queries for notable issues that require your attention. The Security and Audit dashboard is the home screen for everything related to security in OMS. It provides high-level insight into the security state of your computers. It also includes the ability to view all events from the past 24 hours, 7 days, or any other custom time frame.
References:
https://docs.microsoft.com/en-us/azure/active-directory/active-directory-privileged-identity-management-how-to-configure-security-alerts
https://azure.microsoft.com/en-us/blog/how-azure-security-center-helps-analyze-attacks-using-investigation-and-log-search/
https://docs.microsoft.com/en-us/azure/active-directory/active-directory-conditional-access-azure-portal
https://docs.microsoft.com/en-us/azure/security-center/security-center-managing-and-responding-alerts
Explanation/Reference:
Explanation:
Box 1 (Alerting about access to a privileged role): Azure Privileged Identity Management (PIM)
Azure Privileged Identity Management (PIM) generates alerts when there is suspicious or unsafe activity in your environment. When an alert is triggered, it shows up on the PIM dashboard.
Box 2 (Analyzing attack patterns and trends): Azure Security Center
Every second counts when you are under attack. Azure Security Center (ASC) uses advanced analytics and global threat intelligence to detect malicious threats, and the new capabilities empower you to respond quickly.
Box 3 (Using conditional access policies to secure identities): Azure AD Identity Protection
Security is a top concern for organizations using the cloud. A key aspect of cloud security is identity and access when it comes to managing your cloud resources.
In a mobile-first, cloud-first world, users can access your organization’s resources using a variety of devices and apps from anywhere. As a result of this, just focusing on who can access a resource is not sufficient anymore. In order to master the balance between security and productivity, IT professionals also need to factor how a resource is being accessed into an access control decision. With Azure AD conditional access, you can address this requirement. Conditional access is a capability of Azure Active Directory that enables you to enforce controls on the access to apps in your environment based on specific conditions from a central location.
Box 4 (Visualizing real-time security alerts): Operations Management Suite Security and Audit
The OMS Security and Audit solution provides a comprehensive view into your organization’s IT security posture with built-in search queries for notable issues that require your attention. The Security and Audit dashboard is the home screen for everything related to security in OMS. It provides high-level insight into the security state of your computers. It also includes the ability to view all events from the past 24 hours, 7 days, or any other custom time frame.
References:
https://docs.microsoft.com/en-us/azure/active-directory/active-directory-privileged-identity-management-how-to-configure-security-alerts
https://azure.microsoft.com/en-us/blog/how-azure-security-center-helps-analyze-attacks-using-investigation-and-log-search/
https://docs.microsoft.com/en-us/azure/active-directory/active-directory-conditional-access-azure-portal
https://docs.microsoft.com/en-us/azure/security-center/security-center-managing-and-responding-alerts

