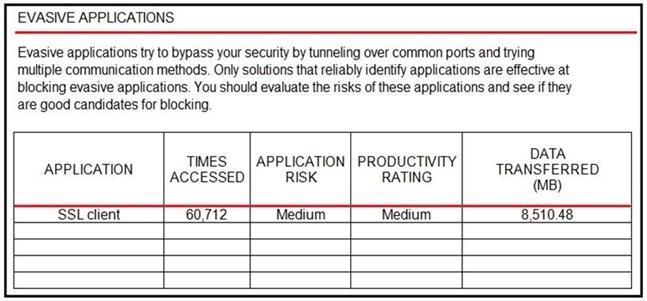
Refer to the exhibit. An administrator is looking at some of the reporting capabilities for Cisco Firepower and noticed this section of the Network Risk Report showing a lot of SSL activity that could be used for evasion. Which action will mitigate this risk?
A. Use SSL decryption to analyze the packets.
B. Use Cisco Tetration to track SSL connections to servers.
C. Use encrypted traffic analytics to detect attacks.
D. Use Cisco AMP for Endpoints to block all SSL connection.

