Refer to the exhibit.
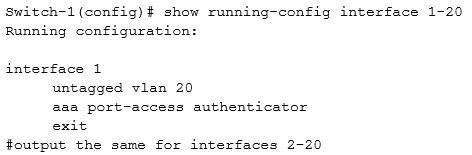
Several interfaces on an AOS-Switch enforce 802.1X to a Radius server at 10.254.202.202. The interface 802.1X settings are shown in the exhibit, and 802.1X is also enabled globally. The security team have added a requirement for port security on the interfaces as well. Before administrators enable port security, which additional step must they complete to prevent issues?
A. Set 802.1X client limit on the interfaces.
B. Manually add legitimate MAC addresses to the switch authorized MAC list.
C. Enable DHCP snooping on VLAN 20.
D. Enable eavesdropping protection on the interfaces.


It’s B.
When the term “Port Security” is mentioned then you need to revert back to the old system of MAC address limiting. Even though using 802.1X combined with MAC address limiting defeats the purpose, it is what they mean.
Maybe A
aaa port-access authenticator client-limit
Configures user-based 802.1X authentication on the specified ports and sets the number of authenticated devices the port is allowed to learn. For more on this command, see Configuring switch ports as 802.1X authenticators.
https://techhub.hpe.com/eginfolib/networking/docs/switches/RA/15-18/5998-8151_ra_2620_asg/content/ch13s07.html
i will say D instead. DHCP has nothing to do with Port security