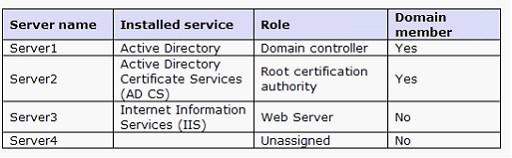
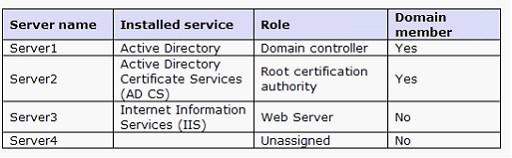
Your network consists of one Active Directory domain that contains servers that use Windows Server 2008 R2. The relevant servers are configured as shown in the following table.
The relevant portion of the network is shown in the exhibit. (Click the Exhibit button.)

Server3 hosts a secure Web site. You want remote users to access the secure Web site by using a Secure Socket Layer (SSL) connection throu the Internet. A server certificate issued by Server2 is installed on Server3.
You need to recommend a solution that will enable the distribution of certificates to the remote users.
The solution must meet the following requirements:
. the certification authority must be automatically trusted.
. Remote users connecting to Server3 must use client certificates issued by Server4.
. A minimum amount of TCP/IP ports must be opened on the firewall that connects the perimeter network and the internal network
Which certification authority should you recommend installing on Server4?
A. enterprise root
B. enterprise subordinate
C. standalone root
D. standalone subordinate
Correct Answer: D
Explanation/Reference:
standalone subordinate – least exposure to risk. (Note: Seeing at the network uses AD, why would this not be enterprise subordinate?)
Stand-alone Microsoft CAs issue certificates for authentication to a secure Web server using Secure Sockets Layer (SSL). They differ from enterprise Microsoft CAs in that they do not require the use of the Active Directory directory service.
Stand-alone CAs do not require Active Directory and do not use certificate templates. If you use stand-alone CAs, all information about the requested certificate type must be included in the certificate request. By default, all certificate requests submitted to stand-alone CAs are held in a pending queue until a CA administrator approves them. You can configure stand-alone CAs to issue certificates automatically upon request, but this is less secure and is usually not recommended, because the requests are not authenticated.
After a root certification authority (CA) has been installed, many organizations will install one or more subordinate CAs to implement policy restrictions on the public key infrastructure (PKI) and to issue certificates to end clients. Using at least one subordinate CA can help protect the root CA from unnecessary exposure.
If a subordinate CA will be used to issue certificates to users or computers with accounts in an Active Directory domain, installing the subordinate CA as an enterprise CA allows you to use the client’s existing account data in Active Directory Domain Services (AD DS) to issue and manage certificates and to publish certificates to AD DS.