Which configuration do you apply to an interface so that it uses port security to learn and commit the first MAC address?
A. Configure the switchport switch-port security violation restrict 1 command.
B. Enable the sticky MAC addresses feature.
C. Enable the static secure MAC addresses feature.
D. Configure the switch for port-security aging type inactivity command.
E. Configure the switchport port-security maximum 1 command.
F. Disable the sticky MAC addresses feature.

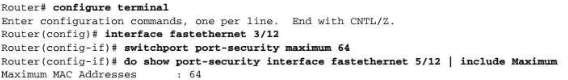

Hi KentSP, if interface has already configured port security, correct answer is E
Wrong answer regrad Cisco port security
https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst6500/ios/12-2SX/configuration/guide/book/port_sec.html
Keyword is learn and commit the first MAC address
Answer is B – sticky feature saves the learn mac address in running config and even after reload mac address learn on that port is still on mac address-table of the switch
Answer E will not save the learn mac address after saving running config and reloading the switch
By default the maximum amount of MAC addresses port-security will learn for a port is one, therefore there is not need to enter switchport port-security maximum 1.
In order to “commit” (save) this first address to the running-config use switchport port-security mac-address sticky
The correct answer is therefore B.
I dont believe the answer is correct, the question ask how to configure Port security in order to learn the first MAC address coming from that port, this is done by the sticky option into the switchport port-security command, so the answer should be B. Also, the explanation has nothing to do with the answer and question.
SW1(config-if)#switchport port-security mac-address sticky