Audit logs from a small company’s vulnerability scanning software show the following findings:
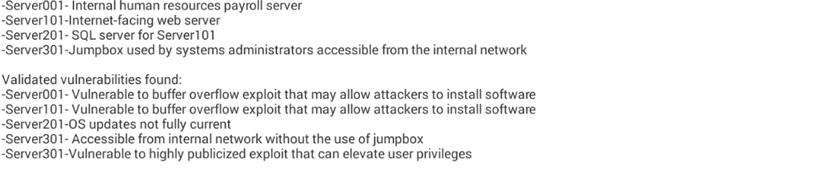
Destinations scanned:
Assuming external attackers who are gaining unauthorized information are of the highest concern, which of the following servers should be addressed FIRST?
A. Server001
B. Server101
C. Server201
D. Server301



B. The question states: “external attackers” Server 101 is connected to the internet and would provide a means for the “external attackers” to gain access.