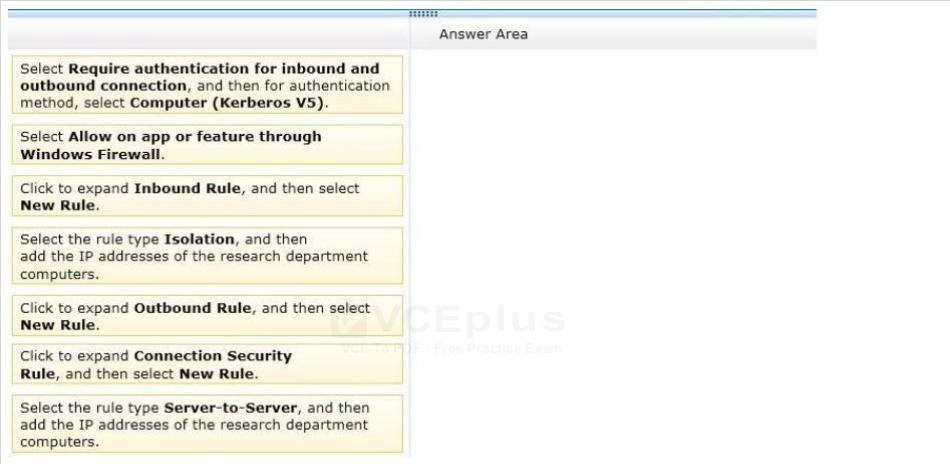
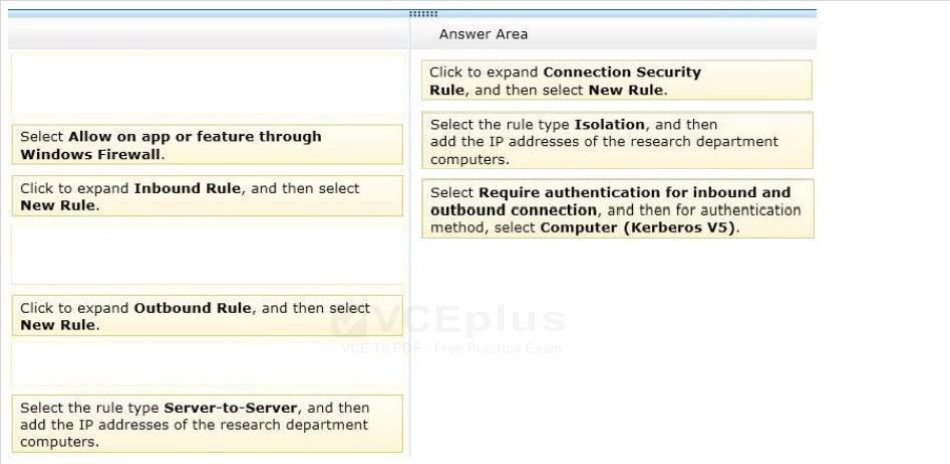
DRAG DROP
You administer desktop computers that run Windows 8 Enterprise and are members of an Active Directory domain.
A new security policy states that all traffic between computers in the research department must be encrypted and authenticated by using Kerberos V5. You need to configure the requested traffic authentication settings by using Windows Firewall with Advanced Settings.
Which three actions should you perform in sequence?
Select and Place: