You administer Windows 8.1 client computers in your company network. A computer that is used by non-administrator users has a directory named C: Folder1.
A shared collection of Microsoft Excel files is stored in the C:Folder directory, with non- administrator users being granted modify permissions to the directory.
You discover that some files have been incorrectly modified by a user.
You need to determine which user made changes to the directory’s folder’s files.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Set local policy: Computer ConfigurationWindows SettingsSecurity SettingsLocal PoliciesAudit PolicyAudit object access to Failure.
B. From the Auditing Entry for Folder1, set the Principal to Guests, and then set the Type to Failure for the Modify permission.
C. From the Auditing Entry for Folder1, set the Principal to Everyone, and then set the Type to Success for the Modify permission.
D. Set local policy: Computer ConfigurationWindows SettingsSecurity SettingsLocal PoliciesAudit PolicyAudit object access to Success.
Correct Answer: CD
Explanation/Reference:
We must audit for success, as we want to know which user has modified the file. http://technet.microsoft.com/en-us/library/cc776774%28v=ws.10% 29.aspx Audit object access
This security setting determines whether to audit the event of a user accessing an object--for example, a file, folder, registry key, printer, and so forth-- that has its own system access control list (SACL) specified.
If you define this policy setting, you can specify whether to audit successes, audit failures, or not audit the event type at all. Success audits generate an audit entry when a user successfully accesses an object that has an appropriate SACL specified. Failure audits generate an audit entry when a user unsuccess- fully attempts to access an object that has a SACL specified.
https://blogs.manageengine.com/product-blog/eventloganalyzer/2012/06/20/object-access-auditing-simplified-find-the-who-what-where-when-of-file-folder-access.html
Object Access Auditing Simplified Find the ‘Who, What, Where, When’ of File & Folder Access Most administrators face the challenge of knowing what actually happened to their files and folders who accessed them, deleted them, edited them, moved them, where the files and folders went, etc. Object access auditing can help administrators to meet this challenge head-on.

If you do not enable the above setting, you will have no record when a file or folder was accessed. Most administrators would like to know only the failure attempts when someone tries to access the file or folder but failed because of improper permission. But it is highly recommended to enable both failure attempts and success attempts. The reason for enabling success attempts is that sometimes hackers can use administrator privilege and gain access to confidential files and folders.
Your enterprise will have crucial data stored in files and folders such as financial data, employee data, patient records, bank account data, etc. The next step is to go to such files and folders to enable auditing on them. Each file / folder’s auditing settings must be modified to include those users you wish to audit.
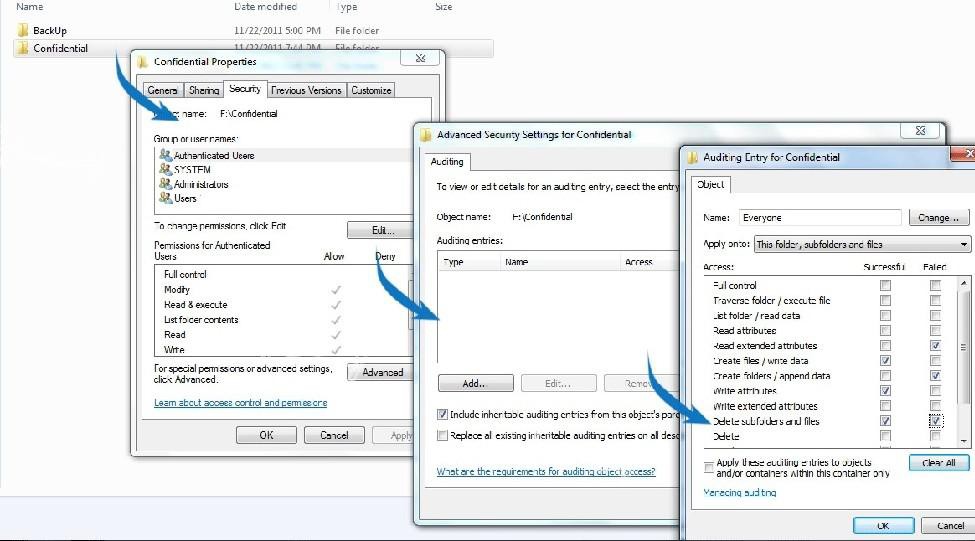
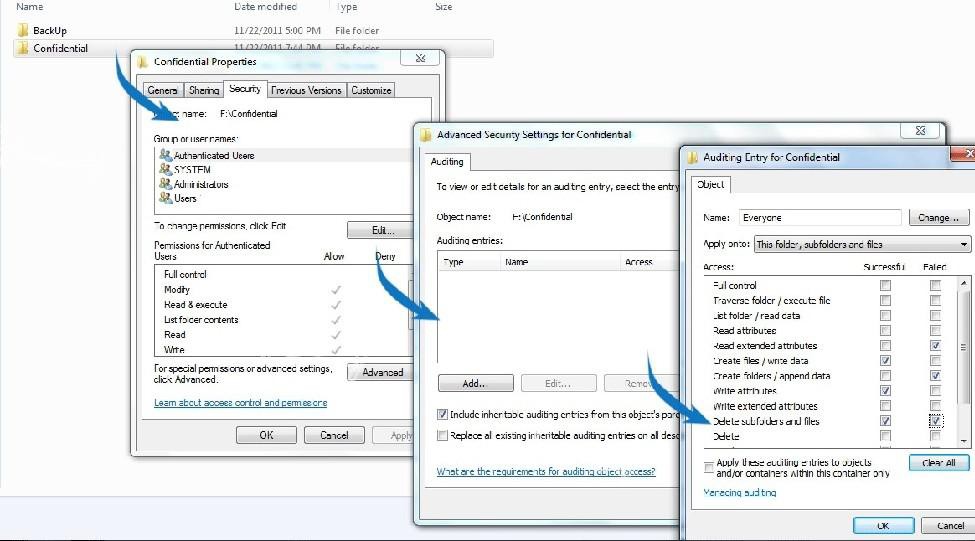
These are enabled in Properties->Security->Advanced->Auditing. If you want to audit all access events by everyone, add everyone group, and select Success>Full Control. (See Screen Shot Below)
Note:
Select the attributes based on your requirement. Delete and Modify attributes are most recommended. Enabling all the attributes to users will flood the event viewer in few seconds, and consume more bandwidth. So judiciously select the attributes required for your auditing needs.
There are no objects configured to be audited by default. Once this auditing setting for an object is configured, log entries on access attempts (Successful and Failed) start getting recorded and you will be able to view the object access related events in the security log in Event Viewer. (See Screen Shot Below)

The events must be opened up individually to inspect their contents, which is a painful process and is totally impossible in an IT enterprise network.