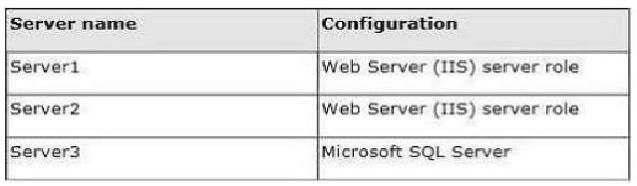
Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2008 R2. The domain contains three servers that run Windows Server 2012. The servers are configured as shown in the following table.
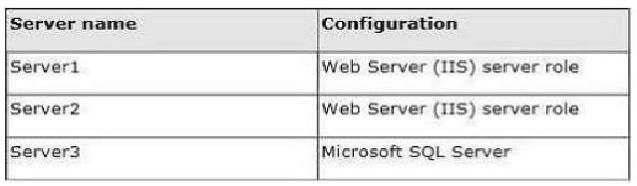
Server1 and Server2 are configured in a Network Load Balancing (NLB) cluster. The NLB cluster hosts a website named Web1 that uses an application pool named App1. Web1 uses a database named DB1 as its data store. You create an account named User1.
You configure User1, as the identity of App1. You need to ensure that contoso.com domain users accessing Web1 connect to DB1 by using their own credentials.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Configure the delegation settings of Server3.
B. Create a Service Principal Name (SPN) for User1.
C. Configure the delegation settings of User1.
D. Create a matching Service Principal Name (SPN) for Server1 and Server2.
E. Configure the delegation settings of Server1 and Server2.
Correct Answer: BE
Explanation/Reference:
Explanation:
To enable impersonation to connect to the database server, the delegation settings for constrained delegation must (computer only trust for delegation to specified services) can be configured. Subsequently, the service principal name can be specified for the identity of the application pool as a delegate service.
The role of the service principal name to authenticate on SQL Server, if an application opens a connection and uses Windows authentication, passes the SQL Server Native Client to SQL Server computer name, -Instanznamen and optionally an SPN. If the connection passes an SPN, it is used without modification.
When the connection is no SPN, a default service principal name is created based on protocol, server name and instance name used. In both scenarios, the Service Principal Name is sent to the Key Distribution Center to a security token for retrieve authenticate the connection. If no security token can be retrieved using NTLM authentication.
A Service Principal Name (SPN, Service Principal Name) is the name that uniquely identifies a client about an instance of a service. The Kerberos authentication service can an SPN to authenticate a service use. When a client wants to connect to a service, it locates an instance of the service, posted an SPN for that instance, connects to the service and transfers the SPN to authenticate to the service.
The preferred method for authenticating users at SQL Server is Windows authentication. Clients that use Windows authentication to authenticate with NTLM or Kerberos. In an Active Directory environment, Kerberos authentication is always performed first. The Kerberos authentication for SQL Server 2005 clients that are using named pipes, not available.
References:
https://docs.microsoft.com/en-us/microsoft-desktop-optimization-pack/appv-v4/how-to-configure-the-server-to-be-trusted-for-delegation
https://technet.microsoft.com/en-us/library/cc961723.aspx