A penetration tester conducted a discovery scan that generated the following:
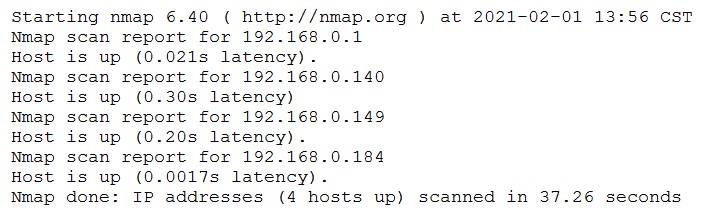
Which of the following commands generated the results above and will transform them into a list of active hosts for further analysis?
A. nmap -oG list.txt 192.168.0.1-254 , sort
B. nmap -sn 192.168.0.1-254 , grep “Nmap scan” | awk ‘{print S5}’
C. nmap –open 192.168.0.1-254, uniq
D. nmap -o 192.168.0.1-254, cut -f 2

