Your network contains a single Active Directory domain.
All client computers run Windows Vista Service Pack 2 (SP2).
You need to prevent all users from running an application named App1.exe.
Which Group Policy settings should you configure?
A. Application Compatibility
B. AppLocker
C. Software Installation
D. Software Restriction Policies
Explanation/Reference:
http://gpfaq.se/2007/09/30/how-to-using-software-restriction-policies/
How-to: Using Software Restriction Policies
Using SRP is not that common today and what I will write here is a small how-to so that you can start trying it today and maybe even sometime soon apply it in your production environment.

First thing to notice is that SRP is a very powerful tool so try in a test-environment before you apply it to users in production.
First you need to choose your default level which you do at Security Levels:

Default when you start using this, the default level is "Unrestricted" which allows all programs to run.
Which means you can use SRP to block specific programs but the power is that you can change this so "Disallowed" is the default level which means you specify which programs you can run (all others are blocked) instead of blocking specific programs.
So to start with change so "Disallowed" is default. Double-click on "Disallowed" and press the button "Set as Default"

This means that all clients affected by this policy now would be able to run anything except what you define as exclusions which you do at "Additional rules":
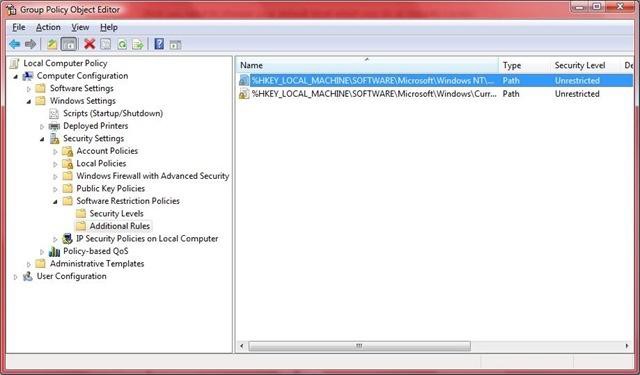
As you can see in the above picture you have two default values already included. These two values are registry paths which makes all programs defined in these two registry paths to unrestricted which of course makes them available to run even if you selected "Disallowed" as your default choice in the above selection at "Security Levels".
There are four different choices on how to enable/disable programs
Hash-rule
Path-rule
Network zo
Certificate-rule
The normal ones to use is HASH or PATH. HASH is always something you should prefer to use since if the user tries to run a program it looks at the hash-value and evaluates if you can run the program or not.
Sometimes when you have different versions of a program for example it might be a problem to use HASH, then you use PATH instead. Also if you don’t have the program installed in the same location on each computer but you know somewhere in the registry where it types the path to the program you can use PATH and use the registry location instead.
I will show you the two ways of allowing Windows Live Messenger to run Hash:

As what you can see above is that it takes the values from the executable and stores the hash-value of the file. When someone tries to run the program the system evaluates this hash-value and compare it with the one you defined and then selecting if you can run the program or not.
Path:

As you can see above is that you need to select the path to the executable. This path needs to be same on each computer you would like to use this on but of course you can use environment variables as I have done in the above picture. You could also use a registry location if you did know where the path to the program where stored.
You can of course also use this to block programs instead of allowing them. This is not really the preferred method on how to use SRP but fully functional.
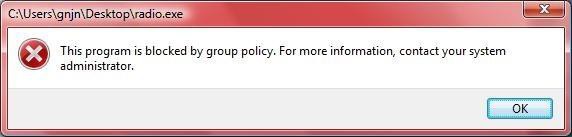
On my computer I have "Unrestricted" as my default and I added an application on my desktop named radio.exe as "Disallowed"

So the result if I’m trying to run the file is:
As conclusion you can see that this is a powerful way of giving your users minimal rights in the system with the result that your users will have a large problem messing up the computer 🙂
This only covers some parts of SRP. For example local administrators also get these rules but that you can exclude in the "Enforcement" choice and also dll-files are excluded by default but you can change that too. Make sure to try this in a safe environment before applying it to production as you might get a big headache if you have made some wrong turns in setting this up. 🙂

