The following are the logs of a successful attack:
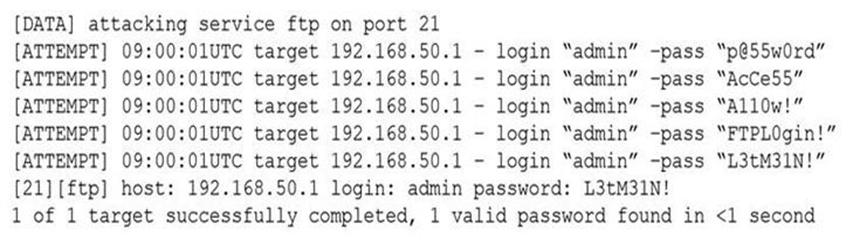
Which of the following controls would be BEST to use to prevent such a breach in the future?
A. Password history
B. Account expiration
C. Password complexity
D. Account lockout
The following are the logs of a successful attack:
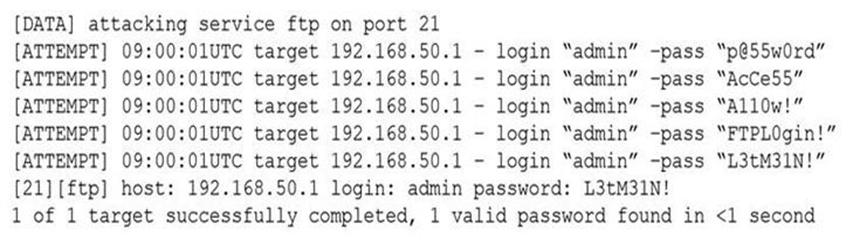
Which of the following controls would be BEST to use to prevent such a breach in the future?
A. Password history
B. Account expiration
C. Password complexity
D. Account lockout