Refer to the exhibit.
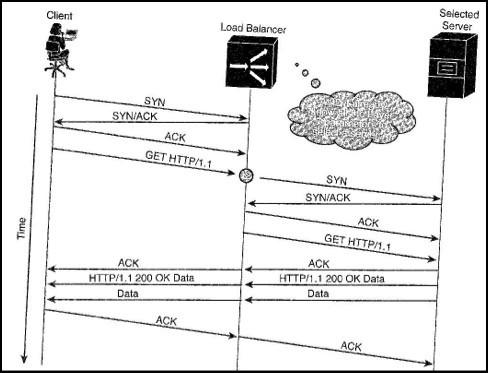
In the figure, the load balancer acts a transparent TCP proxy, and establishes the connection with the client on behalf of the real server. What is this typeof spoofing called?
A. Delayed binding
B. Software-based load balancing
C. Transport proxy
D. Application binding

