A company has client computers that run Windows 8.1. All client computers allow incoming Remote Desktop connections.
You attempt to connect from COMPUTER1 to COMPUTER2 by using Remote Desktop. Remote Desktop cannot connect to the remote computer. You establish that the firewall settings on COMPUTER2 have not been set to allow incoming connections.
From COMPUTER1, you need to enable Remote Desktop traffic through Windows Firewall on COMPUTER2.
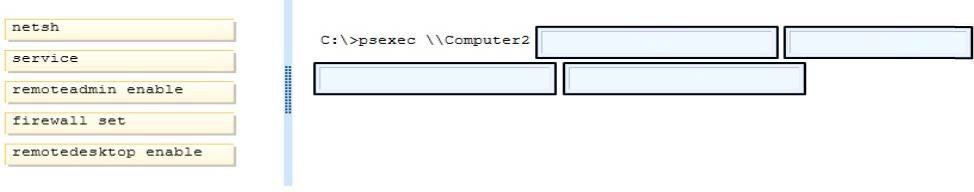
Which commands should you run? (To answer, drag the appropriate command or commands to the correct location or locations in the answer area. Commands may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.)
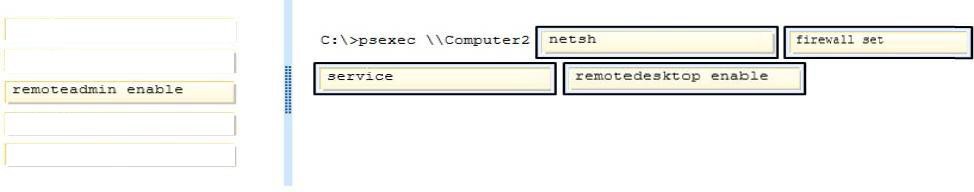
Correct Answer:
Explanation/Reference:
Ref: http://docs.oseems.com/operatingsystem/windows/firewall-command
Explanation:
http://technet.microsoft.com/en-us/sysinternals/bb897553.aspx
PsExec
PsExec is a light-weight telnet-replacement that lets you execute processes on other systems, complete with full interactivity for console applications, without having to manually install client software. PsExec’s most powerful uses include launching interactive command-prompts on remote systems and remote-enabling tools like IpConfig that otherwise do not have the ability to show information about remote systems.
http://ss64.com/nt/psexec.html
PsExec Syntax
psexec \computer[,computer[,..] [options] command [arguments]
http://technet.microsoft.com/en-us/library/cc771046%28v=ws.10%29.aspx
Netsh Commands for Windows Firewall
The Netsh commands for Windows Firewall provide a command-line alternative to the capabilities of the Windows Firewall Control Panel utility. By using the Netsh firewall commands, you can configure and view Windows Firewall exceptions and configuration settings.
.. Netsh firewall
The following sections describe each command and its syntax.
..
set service
Enables or disables the pre-defined file and printer sharing, remote administration, remote desktop, and UPnP exceptions.
Syntax
set service [ type = ] { fileandprint | remoteadmin | remotedesktop | upnp | all } [ [ mode = ] { enable | disable } ] [ [ scope = ] { all | subnet | custom } ] [ [ addresses = ] { IPAddress | IPRange | Subnet | localsubnet }[,…] ] [ [ profile = ] { current | domain | standard | all } ]
Parameters
[ type = ] { fileandprint | remoteadmin | remotedesktop | upnp | all }
Required. Specifies the service whose pre-defined rules are enabled or disabled. The value must be one of the following:
fileandprint. The file and printer sharing service.
remoteadmin. The ability to remotely administer a computer running Windows. remotedesktop. The ability to use a Terminal Services client such as Remote Desktop. upnp. Universal Plug-and-Play protocol for networked devices.
all. All of the above services.
[ [ mode = ] { enable | disable } ]
Specifies whether this exception is currently applied and active on the local computer. The default value is enable.
[ [ scope = ] { all | subnet | custom } ]
..
[ [ addresses = ] { IPAddress | IPRange | Subnet | localsubnet }[,…] ]
..
[ [ profile = ] { current | domain | standard | all } ]