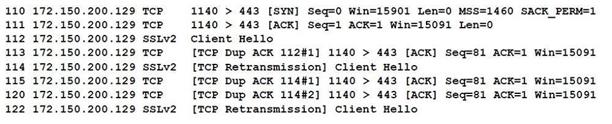
When reviewing network traffic, a security analyst detects suspicious activity:
Based on the log above, which of the following vulnerability attacks is occurring?
A. ShellShock
B. DROWN
C. Zeus
D. Heartbleed
E. POODLE
CS0-002: CompTIA CySA+ ExamFULL Printable PDF and Software. VALID exam to help you PASS. |
 |


I really don’t get how the pcap has no server response. With POODLE and DROWN there should be a client key exchange or a change cipher.
I would call this example “incomplete” or “none of the above” and click POODLE as my answer b/c I had to choose something.
https://enterprisedt.com/blogs/discussion/drown-vs-poodle/
According to this, the answer seems to be POODLE.
https://drownattack.com/
The DROWN (Decrypting RSA with Obsolete and Weakened eNcryption) attack is a cross-protocol security bug that attacks servers supporting modern TLS protocol suites by using their support for the obsolete, insecure, SSL v2 protocol to leverage an attack on connections using up-to-date protocols that would otherwise be secure.[1][2] DROWN can affect all types of servers that offer services encrypted with TLS yet still support SSLv2, provided they share the same public key credentials between the two protocols.[3] Additionally, if the same public key certificate is used on a different server that supports SSLv2, the TLS server is also vulnerable due to the SSLv2 server leaking key information that can be used against the TLS server.[3]